CAPABILITIES
Built for the real world.
Designed specifically for operational technology networks where availability beats everything else.
Passive Mirror-Port Analysis
Zero network impact. Rust-based sniffer with AF_PACKET/TPACKET_V3 captures traffic at line rate — headers only, no payload, no decryption.
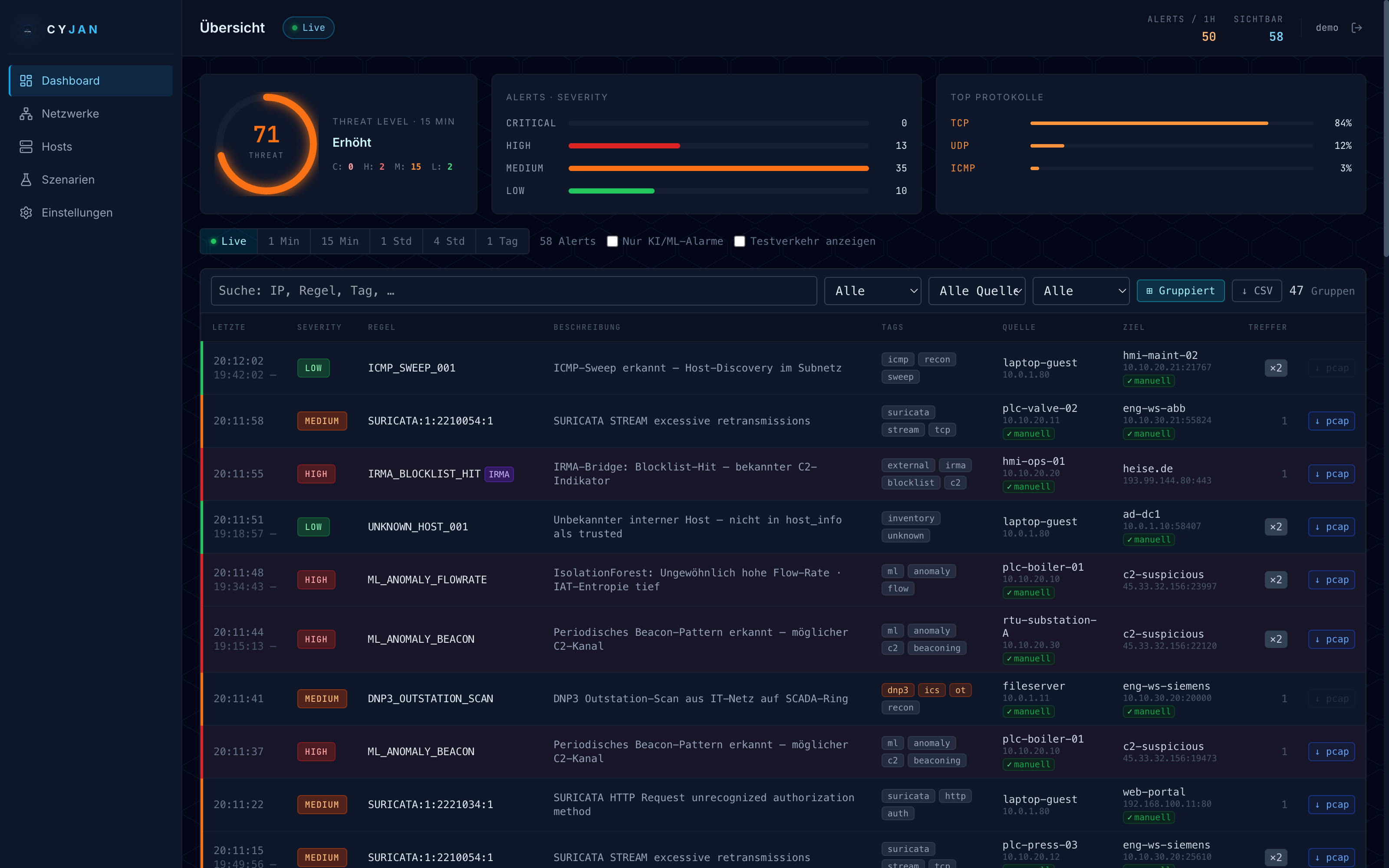
ML Anomaly Detection & Suppression
Isolation Forest with a self-learning feedback loop. Mark alerts as true/false positives and the model retrains automatically. Adaptive suppression downgrades repeat hits on the same rule and bidirectional connection — operators only see real attack patterns, not noise.
OT/ICS Protocol Coverage
Pre-configured rule sets for Modbus TCP, DNP3, EtherNet/IP, BACnet, and S7. OT tags get orange highlighting and auto-escalated severity.
Real-time WebSocket Dashboard
Live alert feed with threat-level gauge, connection graph, PCAP download per alert, enrichment (GeoIP, ASN, DNS), and CSV export.
Suricata Integration
Optional parallel detection engine. ~40,000 Emerging Threats rules plus OT/ICS rule sets from Digital Bond and Positive Technologies — live reloadable.
IRMA Bridge
Integrates external IRMA IDS alerts into the unified feed. REST polling with automatic token renewal — external alarms appear as first-class citizens.
PCAP Evidence Store
Every alert stores a Wireshark-compatible PCAP (headers only) in MinIO — download directly from the alert detail view for forensic investigation.
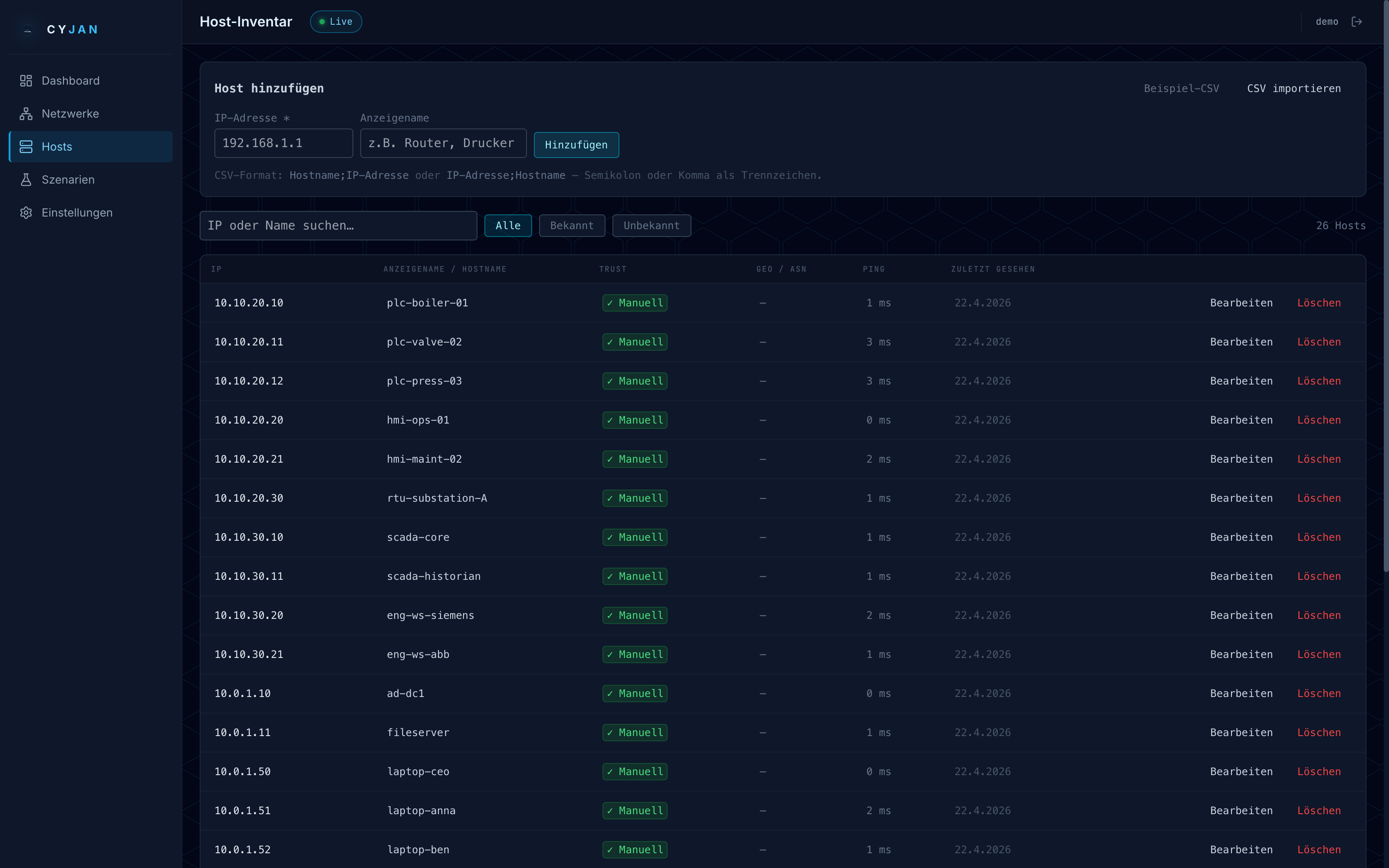
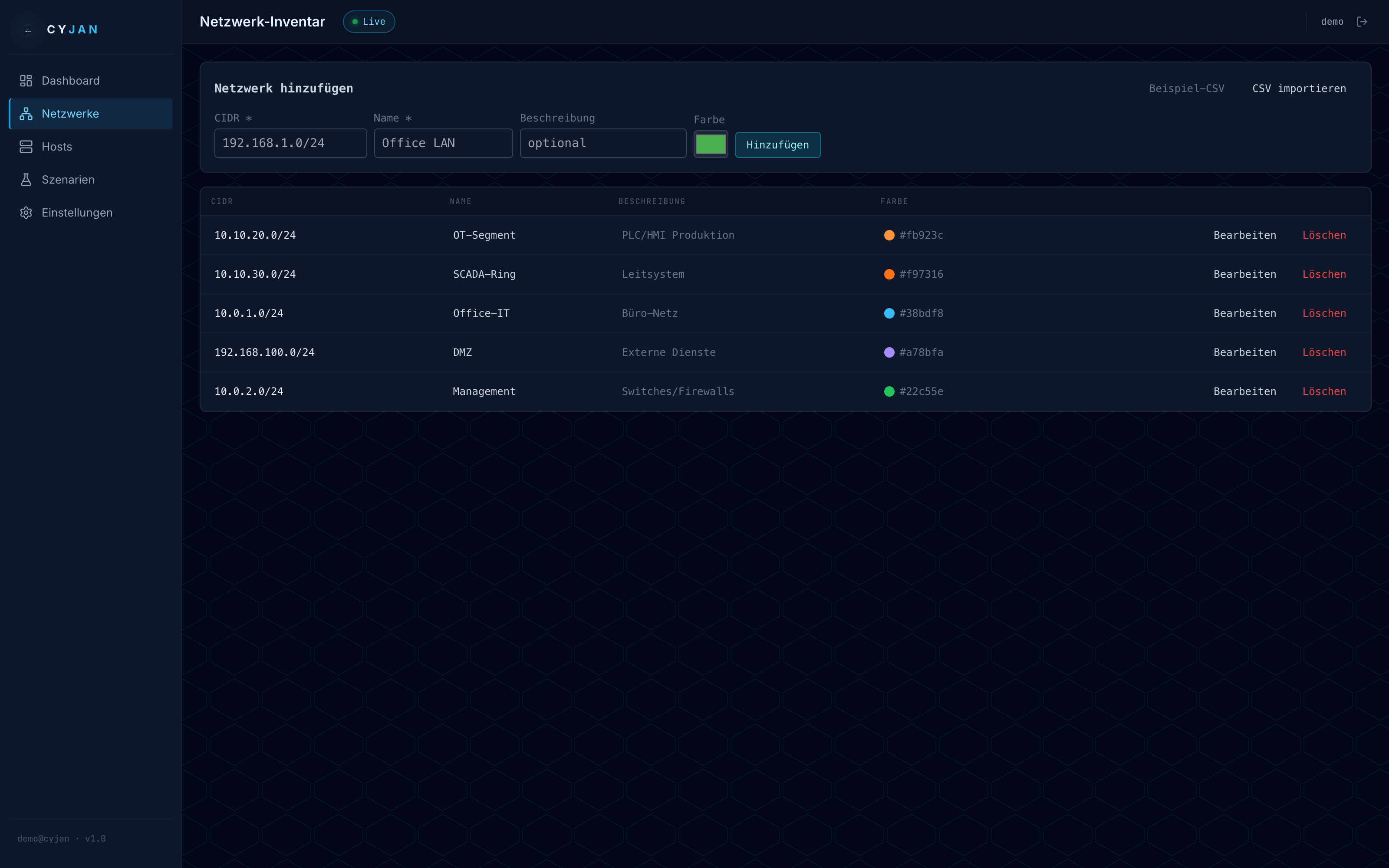
Host Trust System
Known network and host inventory with CSV bulk import, GeoIP/ASN enrichment, and automatic unknown host alerts — with Redis caching for speed.
Debian Live ISO
Plug in, boot, done. First-boot wizard configures interface, IPs, and passwords. Automatic system updates with ids-update. No OS admin skills needed.
Automatic CMDB Sync
Bidirectional iTop / TeemIP integration — imports subnets, hosts, and CI records into the trust system, and pushes newly-discovered unknown hosts back to the CMDB. Manual entries and DNS overrides are preserved by priority; CMDB assets get the ✓ iTop badge.
Full-Blown Enrichment Service
Every alert is post-processed with reverse DNS, ICMP reachability, MaxMind GeoIP/ASN, known-network containment, and host-trust lookup. Redis-cached for sub-second response and streamed live over WebSocket as alert_enriched updates.
Rich FastAPI · OpenAPI
Complete REST surface with interactive Swagger at /api/docs, ReDoc, and an OpenAPI JSON spec. JWT plus SAML 2.0 auth, long-lived API tokens, CSV bulk endpoints, and live WebSocket events — built for SIEM, automation, and third-party integration.
OT-Boundary Classification
Every alert is auto-tagged with source and destination zone — OT, IT, Internet — drawn from your known networks (most-specific CIDR wins). A configurable 3×3 priority matrix flags OT↔Internet crossings as P0; weekly reports break down active boundary breaches per zone-pair, top egress talkers, and Geo/ASN.
Aligned with BSI IDS Guideline
Built along the BSI IDS-Leitfaden: passive Mirror-Port / TAP capture (no traffic injection), header-only analysis — no payload, no SSL break-and-inspect (Vertraulichkeit), mTLS between all components, signed package updates, isolated management network and per-component auth (Eigenschutz). Operator-side: redundant pipeline, sub-second WebSocket feed (Verfügbarkeit) and tamper-evident audit log (Nachvollziehbarkeit).
Remote-Taps for vSwitches & Remote Sites
Compact Tap nodes attach to remote physical switch or vSwitch mirror ports and run the full detection pipeline locally — only finished alerts stream to the Master over mTLS-WSS. Survives Master outages via per-Tap SQLite queue with replay-on-reconnect (deduped by alert_id), centrally rule-synced every 5 min. Branch offices and virtualized environments without backhauling raw traffic.